These changes will improve misra.py execution time in the case where we use globally suppressed checks. For example, when using single MISRA rule and suppress others, we could get about twice the execution speed, since most of `MisraChecker' class methods will not be started at all. Some measurements and discussion are available at: https://github.com/danmar/cppcheck/pull/2301
Cppcheck addons
Addons are scripts that analyses Cppcheck dump files to check compatibility with secure coding standards and to locate various issues.
Supported addons
- cert.py Checks for compliance with the safe programming standard CERT.
- misra.py
Used to verify compliance with MISRA C 2012 - a proprietary set of guidelines to avoid such questionable code, developed for embedded systems. Since this standard is proprietary, cppcheck does not display error text by specifying only the number of violated rules (for example, [c2012-21.3]). If you want to display full texts for violated rules, you will need to create a text file containing MISRA rules, which you will have to pass when calling the script with
--rule-textskey. Some examples of rule texts files available in tests directory. - y2038.py Checks Linux system for year 2038 problem safety. This required modified environment. See complete description here.
- threadsafety.py Analyse Cppcheck dump files to locate threadsafety issues like static local objects used by multiple threads.
Usage
Command line interface
cppcheck --addon=cert --addon=y2038 src/test.c
It is also possible to call scripts as follows:
cppcheck --dump --quiet src/test.c
python cert.py src/test.c.dump
python misra.py --rules-texts=~/misra_rules.txt src/test.c.dump
This allows you to add additional parameters when calling the script (for example, --rule-tests for misra.py). The full list of available parameters can be found by calling any script with the --help flag.
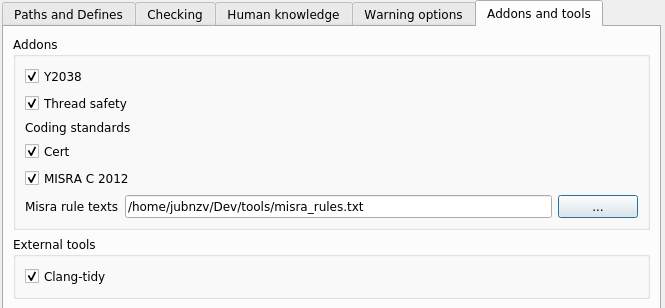
GUI
When using the graphical interface cppcheck-gui, the selection and configuration of addons is carried out on the tab Addons and tools in the project settings (Edit Project File):